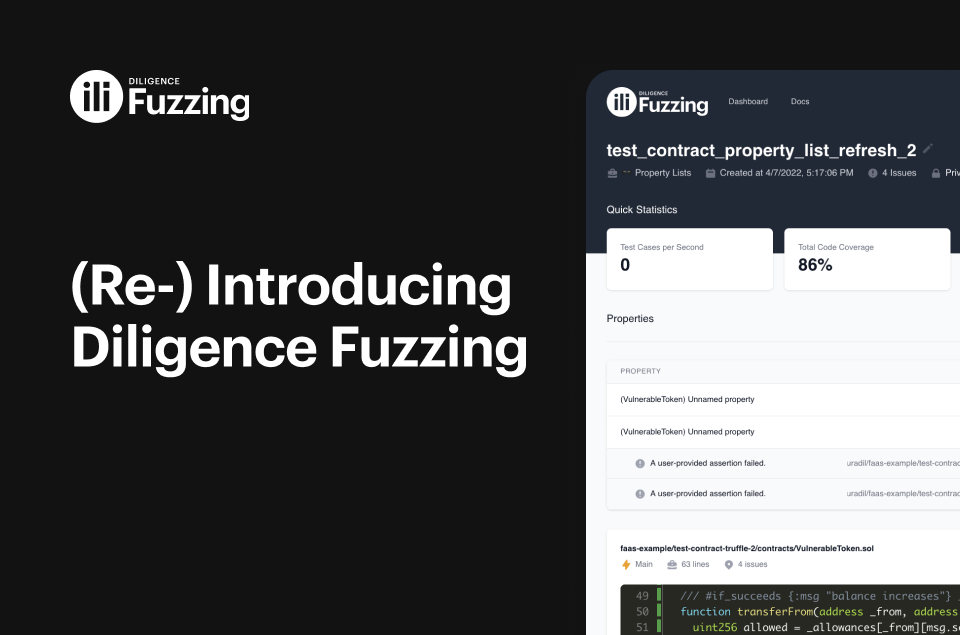
Attention, all auditors and security researchers! We’ve got a new tool for you!
You’re a security researcher and you hate repetitive work. So what do you do? You’ve compiled a nice collection of analysis rules and detection modules that automatically do all the repetitive work for you. Life is great, until, …. You’ve got 100+ modules, some for slither, others for semgrep and things are getting out of hand! You have to spend time writing scripts to run the right modules at the right time, and it’s impossible to even keep track of what you can automatically detect.