ConsenSys Diligence Ethereum Hacking Challenge #2
ConsenSys Diligence is releasing a couple CTF challenges. The first one (“Ethereum Sandbox”) took advantage of changes introduced in the Constantinople upgrade. It was solved by samczsun.
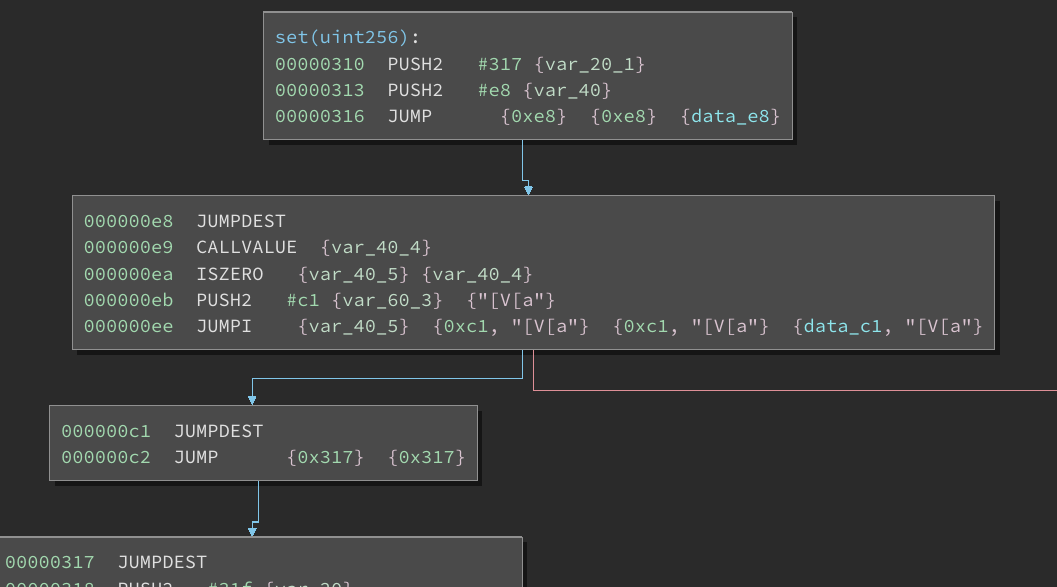
The second challenge is called Rop EVM. Read some bytecode and write an exploit. It is at 0xEfa51BC7AaFE33e6f0E4E44d19Eab7595F4Cca87.
Exploit the contract and extract the 0.05 ether. There’s also a 100 DAI bounty up for grabs. The rules for winning the bounty are the same as last time:
-
If you’re first to extract the ETH and post a write-up on how you did it, you win the bounty (you will need to prove ownership of the attacker’s address — with this contract, if you are not careful, it is possible to send the ETH to an address that you do not control)
-
If you’re not first to extract the ETH but solved the challenge, you can still post a write-up. In case the original thief does not claim the bounty, we will pick the best write-up as the winner.
If you have any questions, head to the MythX Discord. Good luck and have fun!
UPDATE
Congratulations to samczsun for solving this challenge as well! Take a look at his fantastic writeup. Or extract the creation bytecode and continue to solve without the promise of a prize!
Thinking about smart contract security? We can provide training, ongoing advice, and smart contract auditing. Contact us.